TI IOT
The idea is to build a network of sensortags communicating over IPv6 (6LoWPAN).
TI Sensortags (CC2650SDK) will be used a nodes TI CC2538 will be configured as a 802.15.4 sniffer
Creating a 802.15.4 sniffer
- you need firmware that could act as a sniffer run on that mote (cc2538): the firmware, you could find on example on contiki folder ($CONTIKI_HOME/examples/cc2538dk/sniffer)
- need software what forward the packet from sniffer to wireshark (available here)
- setup wireshark to read those packet
To build a firmware, one need to install the proper toolchain first. Instructions are available here
Flashing the CC2538
The goal is to create a new firmware and flash it to the cc2538DK
To create the new firmware, let's use a Contiki example (examples/cc2538dk/cc2538-demo.c)
Instructions are available here https://github.com/contiki-os/contiki/tree/master/platform/cc2538dk
On LinuxMint 17.3, I had to do the following:
- Install gcc-arm-none-eabi and libnewlib-arm-none-eabi (this allows to compile the contiki code)
- if system complains about "Could not find the cc2538-bsl script",
To get uniflash running on a 64bits Unix machine, i had to install the following 32 bits packages:
- libgnomevfs2-0:i386
- liborbit-2-0:i386
- libusb-0.1-4:i386
In Mint: apt-get install libgnomevfs2-0:i386 liborbit-2-0:i386 libusb-0.1-4:i386
Plus, uniflash has to be installed as root, otherwise, we can a connection error
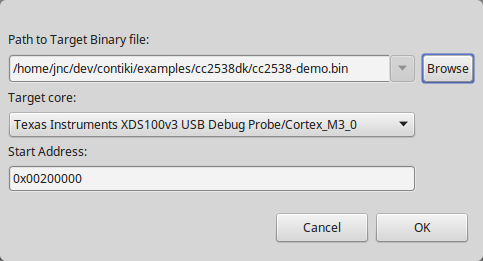
Finally, it is possible to flash using uniflash tool, selecting a binary (.elf) file, specify an address of 0x00200000
SenSniff
SenSniff can be used to get output from the sensortag or CC2538
https://github.com/g-oikonomou/sensniff
- $SENSNIFF_HOM/hosts/python sensniff.py -d /dev/ttyUSB1 -b 460800 -D INFO
python sensniff.py -d /dev/ttyUSB1 -D INFO
python sensniff.py -d /dev/ttyUSB1 -D INFO